The past few weeks have seen attention focused on Tunisia and Egypt in hopes of understanding what role, if any, information and communications technologies (ICTs) are playing in the recent unrest in both countries. While experts and pundits continue to discuss and debate, Iran's efforts at silencing the Green Movement online continue. In my opinion what we are seeing is the latest cyclical flare-up in Iran's “cyber long war” against the Green Movement.
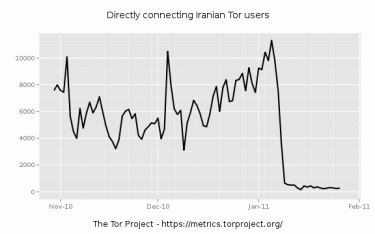
My first post about Tor being blocked in Iran focused on the likelihood that it was regionalized testing that we were seeing. I've confirmed this was indeed the case at the time, and the Tor project's latest blog post on Iran confirms the blockage is now national. The time lag between Iran's testing and implementation of new filtering mechanisms appears to have shortened considerably, perhaps highlighting regime paranoia about “soft war” and the Internet. The latest alpha version of Tor appears to have resolved some connectivity issues for those inside Iran, continuing the cat and mouse game of Internet censorship with the Islamic Republic.
Interestingly, more than a dozen users across northern Iran report that the overall condition of the Internet is “terrible.” They report that anti-censorship tools Freegate and UltraReach as well as some popular VPN packages are being blocked or suffering from extremely slow connectivity. There are also reports that traffic over port 443 (SSL traffic) is extremely slow or being dropped frequently. While Tor may have been the specific target of Iran's latest moves, Iran is an equal opportunity censor.
Iran's cyber long war is not restricted solely to the circumvention front. In the past few weeks many Green Movement activists inside and outside of Iran have been receiving targeted phishing emails. These emails are coming from addresses that appear to be official Google or Yahoo accounts asking the user to click a link and verify their account. The link actually points to a non-Google or Yahoo domain (but which looks official) where the user inputs their password – sending it straight to the regime. The email addresses of targeted activists are often gathered during arrests – computer confiscation is a common occurrence and passwords are often forced out of those unlucky enough to be arrested. Whole networks then become exposed and email accounts targeted for phishing. Once an address is compromised the regime appears to either download/forward all emails or to create email filters which automatically forward a copy of all outgoing and/or incoming email to a regime email address. Since most users don't check their filters often, they can be unaware that they have been compromised and are actively passing all their correspondence to the Iranian government. I strongly recommend everyone in Iran or who has regular contacts with Iran to check their email filters and to change their passwords regularly.
In addition to phishing attacks, the regime has also instigated an old standby – hijacking domain names. Several Green Movement domain names have been hijacked previously, most famously MowjCamp.com which was discussed by Ethan Zuckerman. Less prominent Green Movement sites, however, often just register new domain names instead – leaving many of their users lost and creating a confusing digital landscape for the opposition. In many past cases, including the latest ones that have happened in January, the domain registrars are often in China. Given the close relationship between China and the Islamic Republic and the patterns I have seen with Green domains, I am concerned there could be something more sinister than simple account investigations of “illegal activities” for Green Movement domains registered in China.
Domains are a fertile ground for intimidating the opposition, and not only for hijacking them. This week the website SahamNews.org, associated with opposition leader Mehdi Karroubi, went down from what may have been a hack – the second time in as many months. More interestingly, a new site was launched at nearly the same time called “SahamNew.org” which featured news that Mehdi Karroubi was hospitalized with a heart attack. Observant Internet users quickly discovered this and posted screenshots as evidence that “SahamNew.org” was pointing to the same IP as JavanOnline.ir – a site believed to be controlled by Iran's Revolutionary Guard. This confirms rumors circulating a few months ago that the regime was buying up domain names which were typos or sounded similar to Green domain names and planned to use them to spread false news.

SahamNew.org was created to spread false news about opposition leader Mehdi Karroubi after SahamNews.org went down.
Lastly, and quite sadly, Iran recently executed two men for distributing photos and footage of the 2009 protests in Iran. As I stated in my previous post, what starts out as digital always ends up as human. What's clear is that the regime is playing up their use of the Internet in an “unapproved” way as a subtle way to intimidate other users. The ultimate hope is that Iran's Internet users will censor themselves and that the opposition, which continues to thrive online, will finally wither away. The most efficient form of censorship, after all, is when people censor themselves.
The events discussed in this post give us an opportunity to reexamine what we mean by the phrase “cyber war.” Is it Anonymous DdoSing Egyptian websites? Or is it the Egyptian government shutting down the Internet? What about Stuxnet? Do the executions of Jafar Kazemi and Mohammad Ali Hajaghaei for distributing protest videos fit in? Can a domain name dispute be part of a broader cyber conflict
Although I used the phrase “cyber long war”, I find it troubling. It makes no room for humanity and if read literally it seems to describe conflict between autonomous devices rather than human beings using communications technologies as a proxy for pre-existing disagreements or motivations. There's a lot to be said for how we phrase things: “cyber warfare” is dehumanizing and takes away from the human risks taken by real digital activists (but gives pundits plenty of airtime). It is a convenient way to gloss over uncomfortable truths and create a “digital other” out of both opponents and friends.
The reality is that the events discussed in this post involve real people with human emotions. Each event, taken on its own, is not capable of disheartening a movement, but when taken within the totality of the political and social events in a user's geographical context can contribute to a sense of despair. In that aspect these events can be seen as part of a cyber conflict, but also more broadly as efforts by a regime to digitize the political and social context it has created within its own geographical boundaries. It seems that no matter how hard we try to escape geography, there is always something telling us “we are here, not there”. Unfortunately for many activists in Iran their “here” has become even more hostile since December.




1 comment