A longer version of this post originally appeared on Citizen Lab’s research blog [1].
A new generation of instant messaging apps — offering social networking features, video and photo sharing, e-commerce, gaming, and more — is dominating markets across Asia and moving into countries beyond the region. New research from the Citizen Lab at the University of Toronto investigates government pressures on Asian companies developing instant messaging apps, information controls in the apps, and implications for users.
The Asia Chats [1] project from the Citizen Lab [2] at the Munk School of Global Affairs, University of Toronto is dedicated to analyzing instant messaging (IM) applications used in the region with an initial focus on WeChat [3](Tencent [4], China), LINE [5] (LINE Corporation [6], Japan1 [7]), and KakaoTalk [8] (Kakao Corporation [9], South Korea). Our reports will include technical investigation of censorship and surveillance, assessment of the use and storage of user data, and comparison of the terms of service and privacy policies of the applications. The first report [10] by Senior Security Analyst Seth Hardy examines the implementation of keyword censorship for LINE users based in China and introduces a tool we developed that allows users to circumvent censorship in LINE. A concise overview of our findings follows.
LINE’s rapid growth and privacy concerns
Released in June 2011, popular instant messaging app LINE now has 280 million [11] registered users. Outside of its original market of Japan, LINE has 18 million [12] users in Thailand, 17 million [13] in Taiwan, and 14 million [14] in Indonesia. In December 2012, LINE launched a Chinese-branded version of the app, Lianwo [15] (连我), in partnership with Qihoo 360 Technology Co., Ltd [16].2 [17] The head of LINE’s Chinese division has said that [18] they aim to make it the second biggest mobile IM company in China, after Tencent’s WeChat.
As more and more people begin to use chat apps like LINE, governments have asserted an interest in monitoring communications over these applications for “criminal activity [19]”. A close look at LINE suggests that the app, intentionally or unintentionally, provides ways for law enforcement to eavesdrop on private communication. Citizen Lab researchers verified that LINE chat traffic is sent unencrypted [20] over 3G networks on the latest version of the client. A person with the capability to intercept these messages can obtain chat history, which includes everything from the date and time of the chat to the content of the chat itself. Although mobile 3G networks are encrypted by default, this encryption is implemented at the carrier level, meaning that Internet service providers (ISPs) and telecoms can potentially decrypt the traffic. Commentators have speculated [20] that LINE may have intentionally left 3G unencrypted to allow authorities to access data at the carrier level.
Regionally-based keyword censorship
On May 20, 2013, Twitter user @hirakujira [21] found a list of 150 blocked keywords [22] within the iPhone version of LINE intended for users based in China. To learn more about how censorship in LINE works we reverse engineered the Android LINE application version 3.9.3,3 [23] downloaded from the Google Play store. We found that when a user’s country is set to China during installation, the censorship function is activated. A list of censored keywords is then downloaded from Naver’s server and messages that contain any of these keywords are blocked.
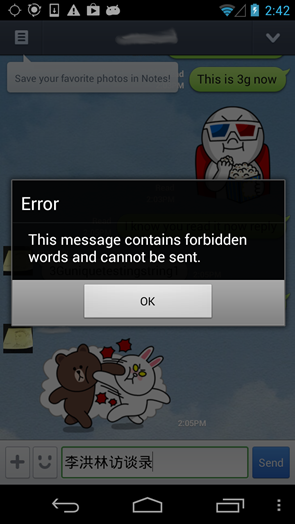
Screen capture of notification users receive when attempting to transmit a keyword on the blocked list.
When LINE is installed, it asks for the user’s country and phone number. The service will send an SMS to this phone number with a four digit code for verification. If the country code of the phone number and the region selected do not match, the program will display an error and suggest the user try again later. Users began sharing instructions [24] for changing their region settings in order to access regionally-specific downloadable content such as stickers (e.g. LINE in Indonesia, for instance, had stickers to celebrate the holy month of Ramadhan.) Downloadable content such as stickers is one of the ways LINE monetizes its service. The previous method [24] for changing regional settings no longer works because newer versions of LINE now encrypt region data, likely to prevent users from changing their region settings and have access to downloadable content that they would otherwise not have access to or have to pay for.
Our research shows that LINE has been capable of censoring specific keywords since at least version 3.4.2, released on January 18, 2013.4 [25] LINE was launched in China in December 2012 and it appears that keyword censorship was enabled soon after the launch. It is likely keyword censorship for users based in China is maintained by Qihoo 360, but exactly how it is managed is not clear. Comparing the mechanism and targeted keywords for censorship in LINE with those used by Qihoo 360 products and WeChat is an interesting area for further research.
LINE’s censored keyword-list includes content related to disgraced former Communist Party of China (CPC) politician Bo Xilai [26], the June 4 1989 [27]crackdown on Tiananmen Square, infighting or factions within the CPC, Falun Gong [28], and various controversies like the fatal Ferrari car crash [29] that involved the son of a party official close to President Hu Jintao and Wen Jiabao family’s secret wealth [30]. Citizen Lab Research Fellow Jason Q. Ng [31] has translated both the original keyword list discovered by @hirakujira, and the latest versions we extracted from Chinese to English and describes the context behind them. The first keyword list discovered by @hirakujira is described in a series of blog posts [32] (full list available here [33]) and the most recent keyword list uncovered by Citizen Lab and translated by Ng is available here [34].
Interestingly, LINE’s censored keyword-list and the lists that we found in our previous research [35] of two other Chinese IM clients, TOM-Skype and Sina UC, are not identical. While some of the topics are the same (e.g. June 4 [36], Falun Gong [37], etc) only 27 keywords out of the 370 in the LINE list [34] are exact matches with the 4,256 unique keywords [38] in the TOM-Skype and Sina UC dataset.
This lack of overlap suggests that [39]no common keyword list was provided to these companies by government authorities. Previous studies on censorship in blog services [40] and search engines [41]localized for the Chinese market have found similar inconsistency between products. Overall, these findings suggest that Chinese companies may be given general guidelines from authorities on what types of content to target, but have some degree of flexibility on how to implement these directives.
How to get around keyword censorship in LINE
As the keyword censorship implemented in LINE is only active if a user’s installation is set to China, it can be disabled if the client is configured to another region (e.g. Canada or the US). To assist users the Citizen Lab has released the LINE Region Code Encrypter Tool [42] for changing regions in the LINE client to disable regionally-based keyword censorship.
Future research
LINE is facing a perennial tension between appealing to a broad user base and complying with government-mandated information control regulations (as in China). These challenges demonstrate the difficulty of operating an application in multiple jurisdictions and the unique characteristics of Asian markets with restrictive communications environments. As Asian IM applications continue to grow in popularity, so too will pressures to enact information controls and disclose user data. The Citizen Lab will continue to analyze the rise and implications of these applications in the Asia Chats series.
For a detailed technical analysis of the findings described here see this report [10]by Citizen Lab’s Senior Security Analyst Seth Hardy.
Asia Chats Research Team: Masashi Crete-Nishihata, Jakub Dalek, Seth Hardy, Andrew Hilts, Katie Kleemola, Irene Poetranto, Jason Q. Ng, Adam Senft, Aim Sinpeng, Byron Sonne, Greg Wiseman.
Footnotes
Naver Corporation [43] (formerly NHN) based in South Korea. Following the success of the application Line Corporation was formed as a subsidiary of Naver.
obtained a business license [44]for LINE to operate in China and it is licensed by LINE to promote and provide its services [45].
3This is the most recent Android version of LINE as of November 14, 2013.
using APK files [46] found at AndroidDrawer.