[1]
[1]Pirate Party demonstrators in Berlin, 2013. Photo by Mike Herbst via Wikimedia Commons (CC BY-SA 2.0)
This Thursday marks the one-year anniversary of the first document leaks by former CIA analyst Edward Snowden. Since June 5, 2013, journalists have uncovered huge volumes of information about both US government and global systems for the surveillance of digital communications.
Here are some of the most significant findings to date:
In his new book about working with Snowden, No Place To Hide, journalist Glenn Greenwald lays out some alarming facts that have been revealed in the year of leaks. In a single 30-day period, the NSA collected…
- Data on more than 97 billion emails and 124 billion phone calls from around the world
- 500 million pieces of data from Germany, 2.3 billion from Brazil, and 13.5 billion from India
- 70 million pieces of metadata in cooperation with France, 60 million with Spain, 47 million with Italy, 1.8 million with the Netherlands, 33 million with Norway, and 23 million with Denmark
- Almost 3 billion telephone calls and emails that had passed directly through US telecom networks. As Greenwald explained, that exceeds the collection of each of the systems from “Russia, Mexico, and virtually all countries in Europe, and roughly equal to the collection of data from China.”
The Snowden report also brought to light a three-tiered hierarchy of NSA partnerships with foreign governments. As reported by Greenwald's book:
TIER 1: Five Eyes is an agreement between the US and United Kingdom, Canada, Australia, and New Zealand to collaborate on global spying while voluntarily restricting their own spying on one another unless specifically requested to do so by a partner country's own officials.
TIER 2: Countries that the NSA works with for specific surveillance projects while also spying heavily on them. These include mostly European countries, some Asian countries, and no Latin American ones.
TIER 3: Countries on which the United States routinely spies but with whom it virtually never cooperates: Brazil, Mexico, Argentina, Indonesia, South Africa, Kenya are some democratic countries that are on the list.
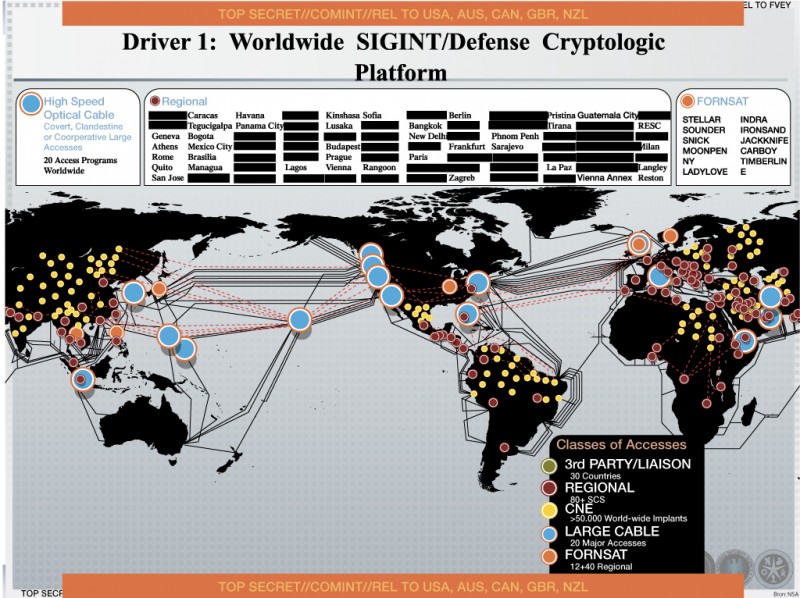 [2]
[2]Worldwide NSA signals intelligence map leaked by Edward Snowden. By US National Security Agency, shared via Wikimedia Commons, released to public domain.
Finally, we now know of the following covert NSA operations:
XKEYSCORE: The software interface through which NSA analysts search vast databases collected under various other operations, XKEYSCORE analyzes emails, online chats and the browsing histories of millions of individuals anywhere in the world. The XKEYSCORE data has been shared with other secret services including Australia's Defence Signals Directorate and New Zealand's Government Communications Security Bureau.
DISHFIRE: The Dishfire operation is the worldwide mass collection of text messages and other phone records, including location data, contact retrievals, credit card details, missed call alerts, roaming alerts (which indicate border crossings), electronic business cards, credit card payment notifications, travel itinerary alerts, meeting information, etc. Communications from US phones have been allegedly minimized, although not necessarily purged, from this database. The messages and associated data from non-US-persons were retained and analyzed.
BULLRUN: Not in and of itself a surveillance program, BULLRUN is an operation by which the NSA undermines the security tools relied upon by users, targets, and non-targets. BULLRUN represents an apparently unprecedented effort to attack security tools in general use.
EGOTISTICAL GIRAFFE: The NSA targeted the Tor browser, a tool enabling Internet users to browse the net anonymously.
MUSCULAR: Launched in 2009, MUSCULAR infiltrates links between global data centers of technology companies such as Google and Yahoo not on US soil. These two companies have responded to MUSCULAR by encrypting these exchanges.
BLARNEY: A program to leverage unique key corporate partnerships to gain access to high-capacity international fiber optic cables, switches and routers throughout the world. Countries targeted by Blarney include: Brazil, France, Germany, Greece, Israel, Italy, Japan, Mexico, South Korea, and Venezuela as well as the European Union and the United Nations
CO-TRAVELER: Under this operation, the US collects location information from global cell towers, Wi-Fi, and GPS hubs. This information is collected and analyzed over time, in part in order to determine a target’s traveling companions.
Overwhelmed by these facts and figures? Itching to do something about it? Check out the international campaign against mass surveillance [3], led by the Electronic Frontier Foundation, Privacy International, and a coalition of Internet policy and human rights experts from around the world. Sign the petition, plan a local event, and learn ways to pressure your government to respect and protect privacy in the digital age.
A version of this post originally appeared on the Electronic Frontier Foundation website [4].