Stories about Anonymity
To Be or Not to Be Anonymous: How Should Bloggers Decide?
This post was co-authored by Nani Jansen, legal director for the Media Legal Defence Initiative. Should you be anonymous online? If you were giving advice to a blogger, independent journalist, or online activist on this issue, what factors would you want her to consider? Many of us have been through this process, but...
Belarus Bans Tor and Other Anonymizers
Belarus is banning anonymizers, typically used to circumvent government censorship and reach online resources banned inside the country, including many of the opposition websites.
China Slams Messaging App Industry with Real-Name Registration Mandate
Critics believe the new policy is intended to target WeChat. The messaging app's soaring sign-up rates outpaced Sina Weibo in early 2014.
Russia Offers 4 Million Rubles to Crack the Tor Network
Although unlikely, should Russia’s decryption project succeed, it could endanger millions of Internet users whose interest in online anonymity is far from nefarious.
TunnelBear VPN Service Blocked in Venezuela?
On Sunday, March 10, Venezuelan users reported that the VPN service TunnelBear was being blocked. Many reported that its website was inaccessible as well.
Love in the Time of Code Era: A Poem About Secure Communication
"It's been a year you first whispered in my ear that PGP is of no use anymore."
Peru: Congress Passes “Practically Secret” Version of IT Crimes Act
In final deliberations over the controversial IT Crimes Bill, also known as the Beingolea Law, Congress members created and unanimously approved a new version of the bill, leaving no opportunity for public scrutiny of the law.
Queer Pakistan is Blocked: Double-Edged Sword of Media Coverage?
A newly launched website to support Pakistan's LGBT youth has been banned by the authorities. Was Queer Pakistan a victim of its own successful publicity?
How the NSA is Tampering with Encrypted Communications (and how to fight back)
New leaks show that the NSA has gone to extraordinary lengths to secretly undermine secure communications infrastructure online. EFF security experts explain what this means for users and what you can do to keep your online communications private.
China: Real Name Registration May Threaten Ethnic Minorities
Under China's new real name registration policy, Internet users are being asked to submit personal information such as their home address, national ID number, and a photograph, in order to register for social media services. A recent case illustrates how some platforms may be using this new information to discriminate against Uyghurs, an ethnic minority group.
Japan: The Police Don't Want You to Use Tor [UPDATE]
According to an April 18 news report, Japan's National Police Agency may soon urge Internet Service Providers to 'voluntarily' block the use of Tor, the anonymous online communication system. The NPA report carrying this announcement has not been formally released; whether NPA will actually put this move into practice remains unknown.
#FreeRod: Chilean Twitter User Faces Trial for Parody
Chilean billionaire Andrónico Luksic has accused Twitter user Rodrigo Ferrari of “usurpation of identity” for running an account that mocked Luksic. If Ferrari is found guilty, the case could set a disturbing precedent for both free expression and privacy in Chile.
Imgur.com blocked in Azerbaijan?
Popular image-sharing site Imgur.com appears to be blocked in Azerbaijan. There is little evidence that Imgur is popular in Azerbaijan. But a few weeks ago, when hacker group Anonymous released a huge volume of documents leaked from Special State Protection Service of Azerbaijan, a user went through the materials and posted some of the more interesting documents available on Imgur.com. This post details a user's technical investigation of the blocking.
Chinese Hackers Spy on Journalists to Track Sources
In January, the New York Times reported that its computers had been under constant attack by Chinese hackers over the past four months. Shortly thereafter, the Wall Street Journal and the Washington Post also reported that they were targeted by Chinese hackers. The story is familiar to Chinese journalists, who, together with citizen reporters from mainland China, are very vulnerable to hacking and online harassment compared to their peers overseas.
Video Advocacy Races Forward: 2012’s Dangers & 2013’s Solutions
Video is increasingly at the nexus of opportunity and danger for human rights activists. Video helps activists to document, confront, circumvent, and lobby against oppressive authorities—but it also allows those authorities to stalk them. Here's what we think will happen in 2013.
#DELETECONTROL/: Campaign Against Digital Repression
The Humanist Institute for Cooperation, Hivos, in partnership with Global Voices Advocacy, Witness, Mideast Youth and Tactical Technology Collective, are launching #DELETECONTROL/, a campaign to help threatened netizens fight against digital repression.
South Korea: Perspectives on Chinese New Net Control Laws
On December 28, 2012, the Chinese government approved a set of new net control laws that would make it compulsory for internet intermediaries to enforce users' real name registration. In South Korea, a similar online real name registration policy has been in place since 2005. Let's examine the South Korean experiment and see what lessons Chinese netizens can learn from it.
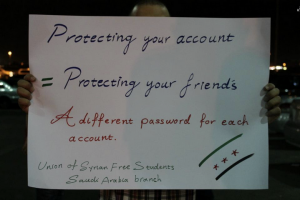
10 New Year's Resolutions to Browse the Internet Safely in 2013
As 2012 draws to a close, dear reader, here at team Advox, we've decided to suggest 10 resolutions for 2013, presented in the form of a review of the tools and strategies to protect yourself online.